November 14th, 2011
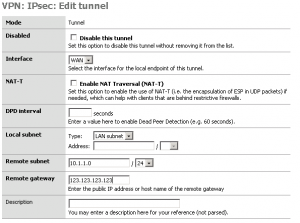
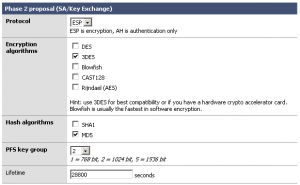
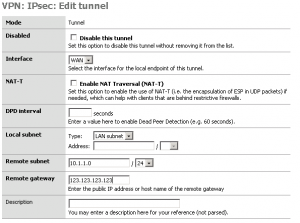
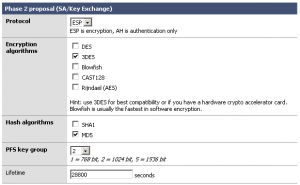
This is an example how to create an site to site VPN between monowall and ASA
Monowall 1.33

ASA
access-list outside_20_cryptomap extended permit ip 10.1.1.0 255.255.255.0 192.168.36.0 255.255.255.0
access-list inside_nat0_outbound extended permit ip 10.1.1.0 255.255.255.0 192.168.36.0 255.255.255.0
nat (inside) 0 access-list inside_nat0_outbound
crypto ipsec transform-set ESP-3DES-MD5 esp-3des esp-md5-hmac
crypto ipsec security-association lifetime seconds 28800
crypto ipsec security-association lifetime kilobytes 4608000
crypto map outside_map 20 match address outside_20_cryptomap
crypto map outside_map 20 set pfs
crypto map outside_map 20 set peer 234.234.234.234
crypto map outside_map 20 set transform-set ESP-3DES-MD5
crypto map outside_map 20 set security-association lifetime seconds 28800
crypto map outside_map 20 set security-association lifetime kilobytes 4608000
crypto map outside_map interface outside
crypto isakmp enable outside
crypto isakmp policy 10
authentication pre-share
encryption 3des
hash md5
group 2
lifetime 86400
tunnel-group 234.234.234.234 type ipsec-l2l
tunnel-group 234.234.234.234 ipsec-attributes
pre-shared-key securepass
August 11th, 2011
NAT a range of ports on a Cisco ASA for FTP use.
In this example I need SSL support, passive ports.
object-group service PassiveFTP tcp
port-object range 60000 60015
static (inside,outside) tcp interface ftp 192.168.1.20 ftp netmask 255.255.255.255
access-list allow_inbound extended permit tcp host host object-group PassiveFTP
access-list allow_inbound extended permit tcp host interface outside eq ftp
static (inside,outside) tcp interface 60000 192.168.1.20 60000 netmask 255.255.255.255
static (inside,outside) tcp interface 60001 192.168.1.20 60001 netmask 255.255.255.255
static (inside,outside) tcp interface 60002 192.168.1.20 60002 netmask 255.255.255.255
static (inside,outside) tcp interface 60003 192.168.1.20 60003 netmask 255.255.255.255
static (inside,outside) tcp interface 60004 192.168.1.20 60004 netmask 255.255.255.255
static (inside,outside) tcp interface 60005 192.168.1.20 60005 netmask 255.255.255.255
static (inside,outside) tcp interface 60006 192.168.1.20 60006 netmask 255.255.255.255
static (inside,outside) tcp interface 60007 192.168.1.20 60007 netmask 255.255.255.255
static (inside,outside) tcp interface 60008 192.168.1.20 60008 netmask 255.255.255.255
static (inside,outside) tcp interface 60009 192.168.1.20 60009 netmask 255.255.255.255
static (inside,outside) tcp interface 60010 192.168.1.20 60010 netmask 255.255.255.255
static (inside,outside) tcp interface 60011 192.168.1.20 60011 netmask 255.255.255.255
static (inside,outside) tcp interface 60012 192.168.1.20 60012 netmask 255.255.255.255
static (inside,outside) tcp interface 60013 192.168.1.20 60013 netmask 255.255.255.255
static (inside,outside) tcp interface 60014 192.168.1.20 60014 netmask 255.255.255.255
static (inside,outside) tcp interface 60015 192.168.1.20 60015 netmask 255.255.255.255
September 20th, 2010
If you made an error in a access list and cannot access the cisco box, what do you do?
An easy solution could be just to restart the box, but then it has to be physically available to you.
Before you make changes, schedue an restart and then if everything works out, cancel the restart.
Commands:
reload in 10
(Reboot in 10 min)
reload cancel
May 12th, 2010
boot system disk0:/asa831-k8.bin
asdm image disk0:/asdm-631.bin
October 13th, 2009
access-list allow_inbound extended permit icmp any any echo-reply
access-list allow_inbound extended permit icmp any any time-exceeded
access-list allow_inbound extended permit icmp any any unreachable
access-group allow_inbound in interface outside
December 30th, 2008
By default you can block domains with a Cisco ASA.
It simply blocks the typed DNS domain names.
Be aware that the IP (ex: http://80.80.80.80) can be accessed until you deny this in an access-list.
regex domainlist1 “\.dating\.dk”
regex domainlist2 “\.facebook\.dk”
regex domainlist3 “\.facebook\.com”
!
access-list inside_mpc extended permit tcp any any eq www
access-list inside_mpc extended permit tcp any any eq 8080
!
class-map type regex match-any DomainBlockList
match regex domainlist1
match regex domainlist2
match regex domainlist3
!
class-map type inspect http match-all BlockDomainsClass
match request header host regex class DomainBlockList
class-map inspection_default
match default-inspection-traffic
class-map httptraffic
match access-list inside_mpc
!
policy-map type inspect http http_inspection_policy
parameters
protocol-violation action drop-connection <— XX
match request method connect
drop-connection log
class BlockDomainsClass
reset log
!
policy-map inside-policy
class httptraffic
inspect http http_inspection_policy
!
service-policy inside-policy interface inside
Block all domains containing the word “facebook” ex: myfacebook.com
regex domainlist1 “.*facebook.*”
December 29th, 2008
By default clients inside a network protected by a Cisco ASA cannot dial up with an PPTP connection.
But if you add this to the configuation it can.
class-map inspection_default
match default-inspection-traffic
!
policy-map global_policy
class inspection_default
inspect pptp
!
service-policy global_policy global
———-
PPTP uses IP protocol 47 (General Routing Encapsulation / GRE) for data.
Allowing connections to be established – port 1723
December 8th, 2008
By default all clients on the LAN can act as a mail server. Maybe you have a “real” mail server. Now a hacker steals one of your client pc’s and uses it to send out SPAM.
How do you configure the firewall so only the “real” mail server can send out emails?
You do it with an access-list on the inside interface. This way you can control the outgoing smtp traffic and only allow one LAN IP to send out emails.
access-list acl_out permit tcp host 10.0.0.2 any eq 25
access-list acl_out deny tcp any any eq 25
access-list acl_out permit ip any any
access-list acl_out permit icmp any any
access-group acl_out in interface inside
June 24th, 2008
The console shows information from the system by default.
It can also be viewed from a telnet session by this command:
terminal monitor
June 11th, 2008
ntp server 213.173.225.86
–
sh ntp status
sh clock
February 24th, 2008
PIX
hostname myPIX
domain-name mydom.dom
ca gen rsa key 1024
ssh 123.123.123.123 255.255.255.255 outside
ssh timeout 60
passwd my_code
ca save all
write mem
ASA
crypto key generate rsa
In ASDM
crypto key zeroize rsa noconfirm
crypto key generate rsa noconfirm
—–
show crypto engine
show crypto ipsec sa
February 11th, 2008
If an error occurs on your network, the professional series of Cisco switches would probably shutdown the the network port where the error is detected.
Even if the error on the network is corrected, the network port is still down. You have to enable it manually.
The switch is able to automatically enable the port. If the root error on the network remains, the port is immediately shutdown again.
To check the configuration, use this command:
show errdisable recovery
If something is disabled, it means you manually have to activate the port if this specific error has occurred.
It can all be done automatically with this commands:
errdisable recovery cause udld
errdisable recovery cause bpduguard
errdisable recovery cause security-violation
errdisable recovery cause channel-misconfig
errdisable recovery cause pagp-flap
errdisable recovery cause dtp-flap
errdisable recovery cause link-flap
errdisable recovery cause gbic-invalid
errdisable recovery cause psecure-violation
errdisable recovery cause dhcp-rate-limit
errdisable recovery cause unicast-flood
errdisable recovery cause vmps
errdisable recovery cause storm-control
errdisable recovery cause loopback
errdisable recovery cause sfp-config-mismat
August 2nd, 2007
One of the most common tasks is to configure a router to deliver trafic from the outside Internet to the inside LAN. How is that done on a PIX or ASA?
1.
Add the basic NAT rule that makes NAT from the outside works.
static (inside,outside) tcp interface 3389 192.168.0.10 3389 255.255.255.255 0 0
In this example Remote Desktop (port 3389) is NAT’ed to 192.168.0.10
If you want to use a different port from the outside just change the line to
static (inside, outside) tcp interface 3390 192.168.0.10 3389 255.255.255.255 0 0
port 3390 is delivered to 192.168.0.10:3389
2.
Now add an access rule that describes who has access. If everyone should have access use this line
access-list allow_inbound permit tcp any interface outside eq 3389
3.
Finally, activate the new access-list to the outside interface.
access-group allow_inbound in interface outside
clear xlate
July 27th, 2007
What do you do if you have three webserveres all listening on port 80 and three public IP’s, but only have one firewall/router?
You do not need three routers but if you have a Cisco ASA it all can be done on that.
1. If a Internet user types 111.222.333.2 he ends up on WEB01. 111.222.333.3 end up on WEN02 and so on.
2. All the webservers acts on the Internet with thire own public IP
All you need is a Static and an access roule.

static (inside,outside) <public ip> <local ip>
access-list allow_inbound permit tcp any host <public ip> eq www
To follow the example above, just add these lines.
access-list allow_inbound permit tcp any host 111.222.333.2 eq www
access-list allow_inbound permit tcp any host 111.222.333.3 eq www
access-list allow_inbound permit tcp any host 111.222.333.4 eq www
static (inside,outside) 111.222.333.2 10.0.0.2
static (inside,outside) 111.222.333.3 10.0.0.3
static (inside,outside) 111.222.333.4 10.0.0.4